






 kapil sharma -
November 27, 2025 -
Technology -
full stack course
full stack developer course
-
390 views -
0 Comments -
0 Likes -
0 Reviews
kapil sharma -
November 27, 2025 -
Technology -
full stack course
full stack developer course
-
390 views -
0 Comments -
0 Likes -
0 Reviews
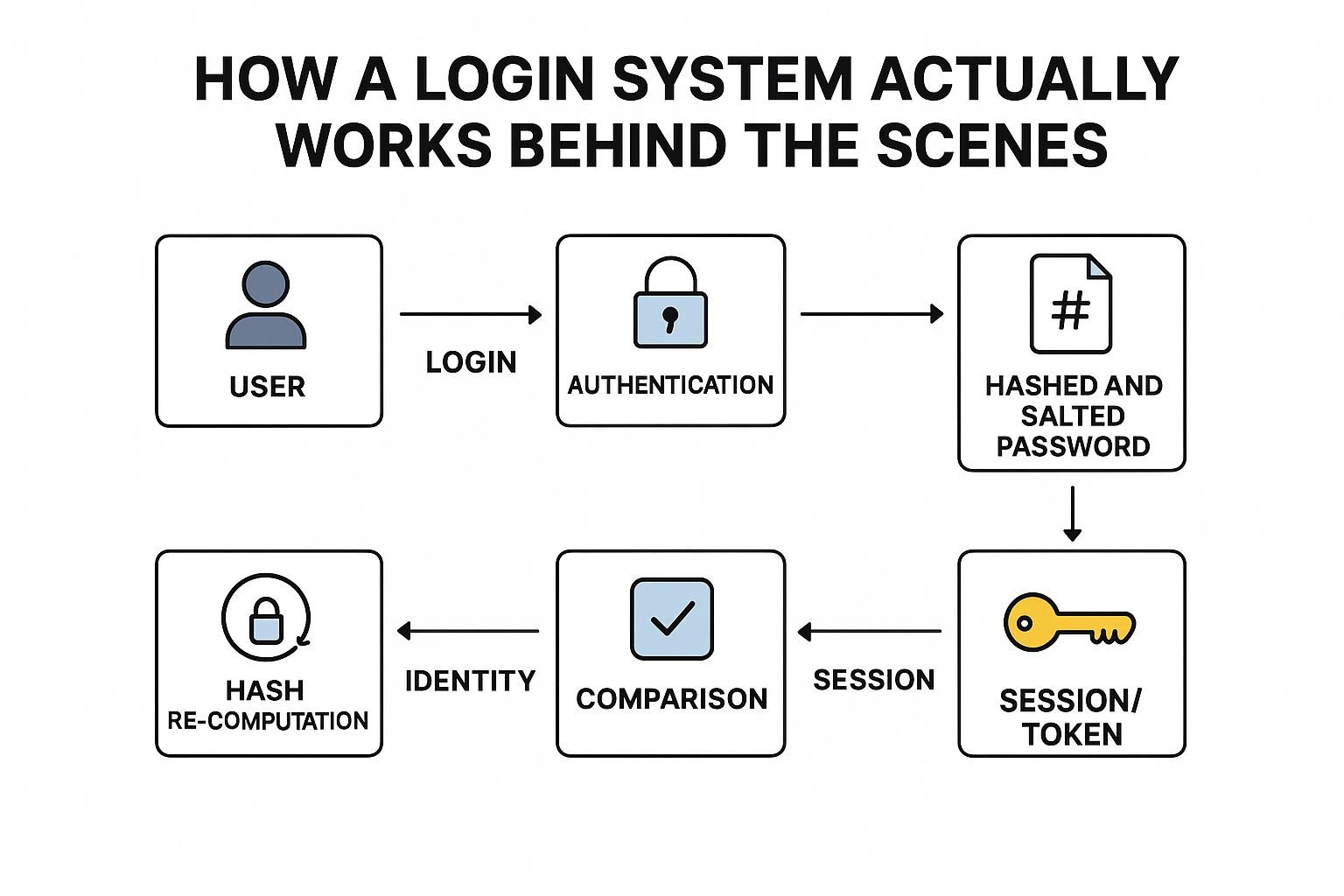
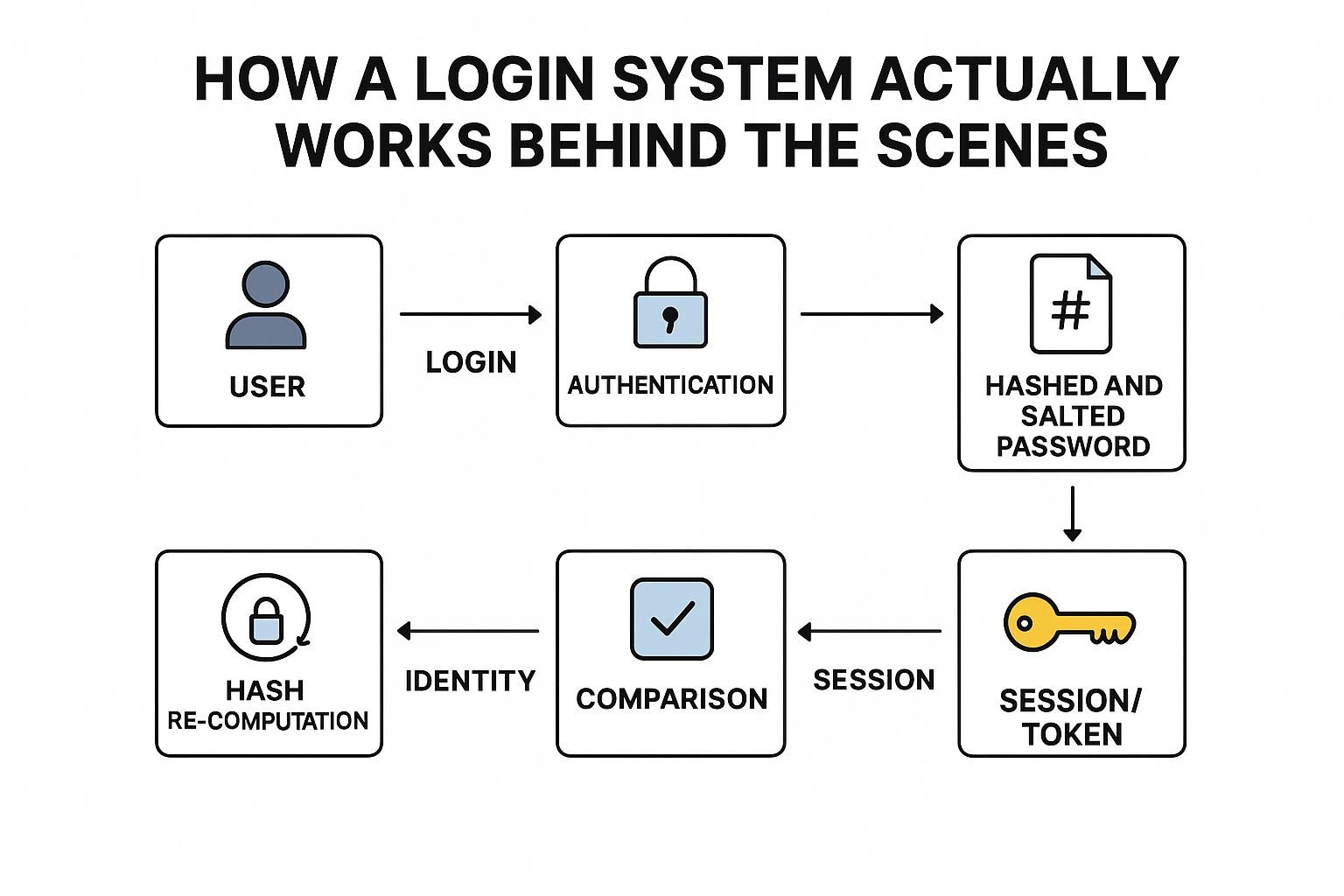
Introduction
The login system is a controlled identity verification pipeline that processes user credentials, checks stored authentication records, verifies integrity, and creates a secure identity session. All this works through a series of backend steps: handling input, running encryption-based checks, generating tokens, or sessions to represent the user state in the system. In Delhi, with the growth of distributed applications, the demand for developers being trained under a Full Stack Developer Course in Delhi has grown to understand how a login mechanism works internally, especially when authentication needs to scale for large platforms.
How Input Moves Through the System Before Authentication?
When a user inputs their login information, the data travels through multiple backend layers before actually checking the password. Firstly, the system establishes a safe connection through HTTPS, wherein everything is encrypted within the environment for safety. Once the request reaches the server, the login pipeline begins its internal process.
First, there is request validation, where the system checks if characters, data format, and structure are as per predefined rules. This process cleans out malicious inputs and ensures that the request does not include suspicious payloads. This step will be done by middleware or a gateway layer that inspects the raw request.
Most companies run big automation environments in Gurgaon, and that is why platforms usually feature advanced systems of request filtering. That partly explains why students of a Full Stack Developer Course in Gurgaon would work with identity throttling tools applied in the production level of applications.
It then checks the metadata of the request: device signature, network origin, and connection traits. This offers an early detection of abnormal behavior before any processing for a username and password.
What Happens When the Password Reaches the Server?
The password submitted then goes to the authentication engine after the initial phases of filtering. The actual password is never stored by a login system. It stores a version of the password, hashed and salted. Hashing is a way of changing the original password into a secure, irreversible string.
Here, the authentication engine retrieves the stored password hash and the salt from secure storage. Commonly, these are kept in a secured database or in a vault of secrets.
Most cloud-based training arrangements, including the Full Stack Developer Online Course, also engage learners in hash algorithms, timing protection, and safe password storage. In the Full Stack Developer Online Course, students will be assigned practical tasks to test how inappropriate hashing or weak storage can break the login workflow.
How Sessions and Tokens Are Formed After Authentication?
The system switches from checking identity to creating identity once the login is validated. The login system needs to create a representation of the user's active state in some form, so the user does not have to log in after every request.
Two major identity models are used by backend systems:
Server-Side Sessions
The server would create a session object comprising user ID, roles, permissions, and session expiry time. This session is stored either in memory or in an external session store like Redis. A unique session ID is sent from the system to the user's browser. In turn, the browser will send this ID to the server in every request, confirming the state of the user.
Token-Based Authentication
Systems using JWT or opaque tokens store identity information within the token itself. The server signs the token with a secure key. A token is stored on the client side. The identity is not set after one logs in; it gets re-verified by the system throughout the session.
Also Visit To Related Courses
Python Full Stack Online Course
Continuous Monitoring and Identity Verification After Login
None of the modern applications treat authentication as a single-point-in-time activity; even after authentication and login, the session's behavior is checked in the background by the system.
Some run behavioral checks where unusual activity will trigger re-validation. Others handle session synchronization whereby identity data is updated across a set of services that would run inside a microservices architecture, making sure that all the services have the correct user roles and access values.
Policy checks also occur in distributed systems: an operation may need to recheck the user's privileges. This may prevent unauthorized actions when roles or permissions are changed during an active session.
Following is a table highlighting some of the major models of identity that are in use in login systems:
Login Identity Models Comparison
|
Identity Model |
Where Data Lives |
Security Strength |
Common Use |
|
Server Sessions |
Server-side store |
High |
Web dashboards, internal systems |
|
JWT Tokens |
Client-side storage |
Medium to High |
Mobile apps, SPAs |
|
Opaque Tokens |
Server validation |
High |
API gateways, zero-trust systems |
|
Federated Identity |
External provider |
High |
Single sign-on flows |
Sum Up
The login system is a structured identity mechanism that comprises several backend layers, which coordinate with each other with the purpose of securely validating users. It receives input, filters it through various validation checks, performs hashing and comparison functions, builds identity sessions or tokens, and monitors user behavior during an active session.

This website uses cookies to ensure you get the best experience on our website.
To learn more about our privacy policy Click here